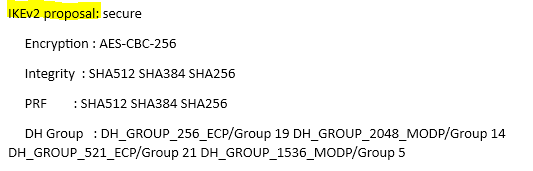
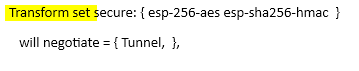
Today, we will be looking at the top few commands that are being mostly used when troubleshooting the IKEv2 IPSEC VPN tunnels. First of all, we will need to disable debugging on the Cisco appliance. Secondly, we are going to enable debugging. Lastly, we will be enabling the feature which will show the debugging messages in the current terminal.
- Disable debugging on the Cisco appliance
undebug all
- Defining the debug condition (in this example, we have used the condition PEER IP | the IP address has been denoted by x.x.x.x)
debug crypto condition peer ipv4 x.x.x.x
- Enable debugging for IKEv2
- debug crypto ikev2
- debug crypto ikev2 error
- debug crypto ikev2 internal
- debug crypto ikev2 packet
- Enable debugging for IPSEC
- debug crypto ipsec
- debug crypto ipsec error
- debug crypto ipsec message
- debug crypto ipsec states
- Enable the terminal monitor to view the DEBUG output with the command: terminal monitor
- Disable the terminal monitor to view the DEBUG output with the command: terminal no monitor