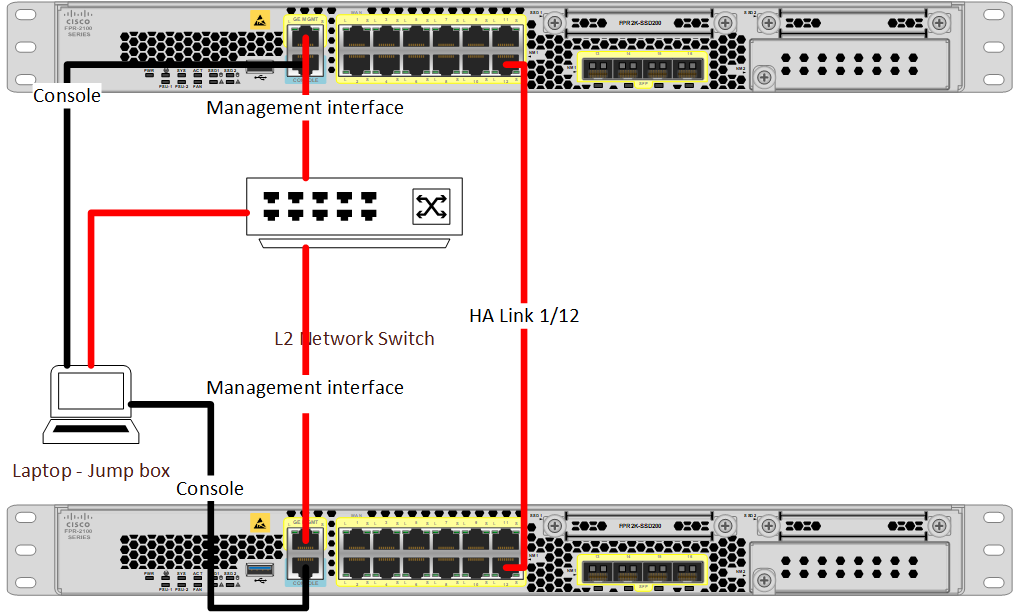
In our example, we will be looking at the initial configuration when setting up the Cisco Firepower 2100 series. As you can see in the below topology, we have used 2 FPR devices connected through the ports 1/12. Also, we have used 2 console connections connected through a basic LAN switch. In this example, the IP assignments are as below.
| IP assignments | Cisco FPR2100-01 | Cisco FPR2100-02 |
| Device management IP | 192.168.111.5 | 192.168.111.6 |
| Subnet | 255.255.255.0 | 255.255.255.0 |
| Default gateway | 192.168.111.1 | 192.168.111.1 |
- Make a console connection with the FPR2100 appliances and connect to the FTD module.
firepower# connect ftd
- Setting up the FTD management IP address on the first FPR appliance
>configure network ipv4 manual 192.168.111.5 255.255.255.0 192.168.111.1
- Setting up the FTD management IP address on the second FPR appliance
>configure network ipv4 manual 192.168.111.6 255.255.255.0 192.168.111.1
- Set the management access type to the local
>configure manager local
- Then, configure the management access. In this example, we have allowed all
>configure https-access-list 0.0.0.0/0
- Finally, make sure that you have entered the correct parameters with the below command
>show network