As Network Engineers, we use packet tracer on both ASA/FTD systems. There are times where we need to run packet tracer to verify the NAT configuration. If you see errors related to RPF (Reverse Path Forwarding), you can simply try using the public IPs instead of private IP addresses. In the below example, the destination IP has been the NAT assigned public IP.
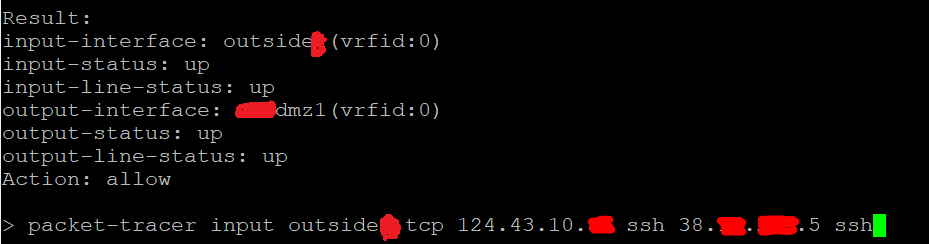
packet-tracer input outside tcp source_public_ip ssh nat_public_ip ssh
If you are not comfortable with the packet tracer, you can refer the guide

